As more and more financial transactions are conducted in digital form each year, financial threats comprise a large piece of the global cyberthreat landscape. That’s why Kaspersky researchers analyze the trends related to these threats and share an annual report highlighting the main dangers to corporate and consumer finances. This report contains key trends and statistics on financial phishing, mobile and PC banking malware, as well as offers actionable recommendations to bolster security measures and effectively mitigate emerging threats
Methodology
In this report, we present an analysis of financial cyberthreats in 2024, focusing on banking Trojans and phishing pages that target online banking, shopping accounts, cryptocurrency wallets and other financial assets. To gain an understanding of the financial threat landscape, we analyzed anonymized data on malicious activities detected on the devices of Kaspersky security product users and consensually provided to us through the Kaspersky Security Network (KSN). Note that for mobile banking malware, we retrospectively revised the 2023 numbers to provide more accurate statistics. We also changed the methodology for PC banking malware by removing obsolete families that no longer use Trojan banker functionality, hence the sharp drop in numbers against 2023.
Key findings
Phishing
- Banks were the most popular lure in 2024, accounting for 42.58% of financial phishing attempts.
- Amazon Online Shopping was mimicked by 33.19% of all phishing and scam pages targeting online store users in 2024.
- Cryptocurrency phishing saw an 83.37% year-over-year increase in 2024, with 10.7 million detections compared to 5.84 million in 2023.
PC malware
- The number of users affected by financial malware for PCs dropped from 312,000 in 2023 to 199,000 in 2024.
- ClipBanker, Grandoreiro and CliptoShuffler were the prevalent malware families, together targeting over 89% of affected users.
- Consumers remained the primary target of financial cyberthreats, accounting for 73.69% of attacks.
Mobile malware
- Nearly 248,000 users encountered mobile banking malware in 2024 – almost 3.6 times more than in 2023 when 69,000 users were affected.
- Mamont was the most active Android malware family, accounting for 36.7% of all mobile banker attacks.
- Users in Turkey were the most targeted.
Financial phishing
In 2024, online fraudsters continued to lure users to phishing and scam pages that mimicked the websites of popular brands and financial organizations. The attackers employed social engineering techniques to trick victims into sharing their financial data or making a payment on a fake page.
We analyzed phishing detections separately for users of our home and business products. Pages mimicking web services accounted for the largest slice of the business pie at 26.56%. The percentage was lower for home users (10.34%), but home users were more likely to be targeted by pages using banks and global internet portals, social media and IMs, payment systems, and online games as a lure. Delivery company scams accounted for 15.17% of attacks targeting businesses, but did not register in the top ten for home users.
TOP 10 organizations mimicked by phishing and scam pages that were blocked on business users’ devices, 2024 (download)
TOP 10 organizations mimicked by phishing and scam pages that were blocked on home users’ devices, 2024 (download)
Overall, among the three major financial phishing categories, bank users were targeted most in 2024 (42.58%), rising a little over 4 p.p. on the previous year. Online stores were of relatively less interest to the fraudsters at 38.15% dropping from 41.65% in 2023. Payment systems accounted for the remaining 19.27%.
Distribution of financial phishing pages by category, 2024 (download)
Online shopping scams
The most popular online brand target for fraudsters was Amazon (33.19%). This should not come as a surprise given Amazon is one of the world’s largest online retailers. With 2.41 billion average monthly visitors and $447.5 billion in annual web sales, up 8.6% in 2024, there is every chance Amazon will retain its dubious honor into 2025.
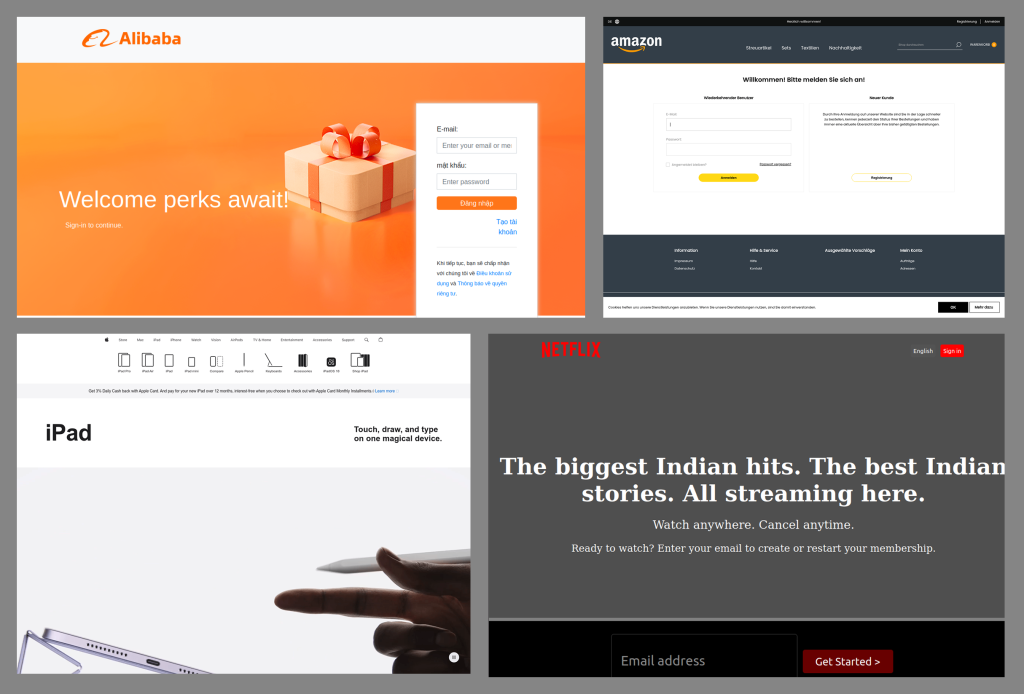
Apple’s share of attacks dropped nearly 3 p.p. from last year’s figure to 15.68%, while Netflix scams grew slightly to 15.99%. Meanwhile, fraudsters’ interest in Alibaba increased, its share going up from 3.17% in 2023 to 7.95% in 2024.
Examples of phishing sites that mimic Amazon, Netflix, Apple and Alibaba
Last year, Louis Vuitton accounted for a whopping 5.52% of all attacks. However, the luxury brand completely slipped out of the top ten in 2024, along with Italian eyewear company Luxottica. Instead, sportswear giant Adidas and Russian e-commerce platform Ozon entered the list with 1.39% and 2.75% respectively. eBay (4.35%), Shopify (3.82%), Spotify (2.84%) and Mercado Libre (1.86%) all stayed in the top ten, with marginal differences from the previous year.
TOP 10 online shopping brands mimicked by phishing and scam pages, 2024 (download)
When looking at fake website content, free prizes and offers that were a little too good to be true once again proved a popular tactic used by scammers. However tempting they may be, most likely, the victim will be the one who pays. Often scammers require “commissions” to get the prize or ask user to pay for delivery. After receiving the money, they disappear.
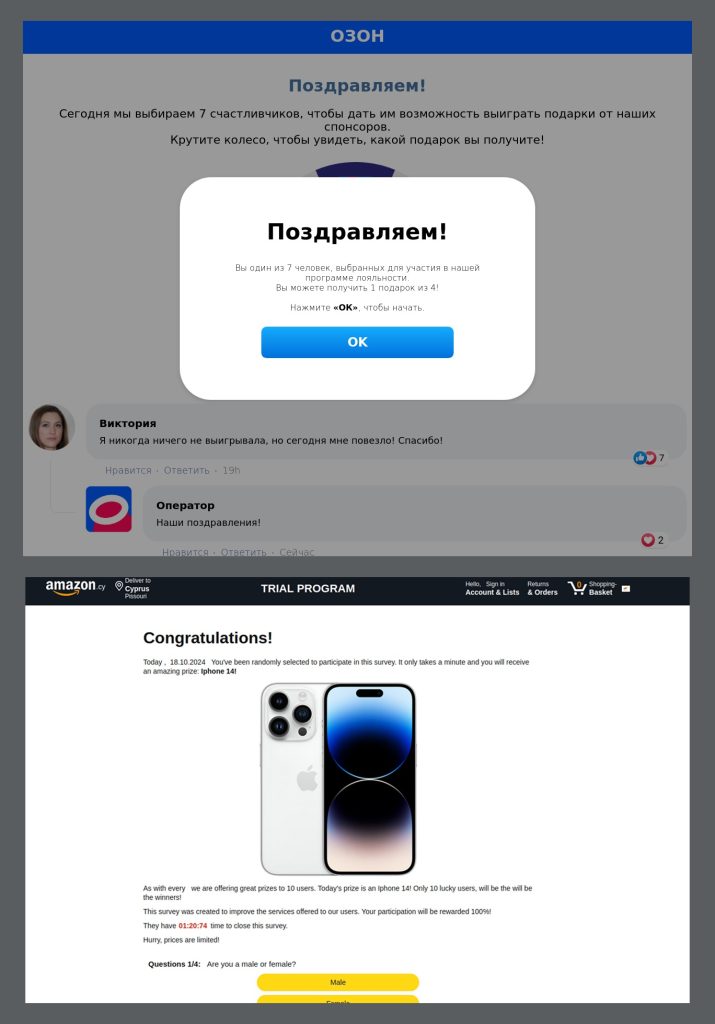
Examples of scam pages offering free prizes
In other cases, precious gifts are used by phishers to trick the user into giving out their credentials. The scheme below offers the victim an Amazon gift card to obtain which they should enter an OTP code on a phishing website. Although such codes are temporary, the scammers may use them to log in to victim’s account or perform a fraudulent transaction as soon as it is entered into the fake form.
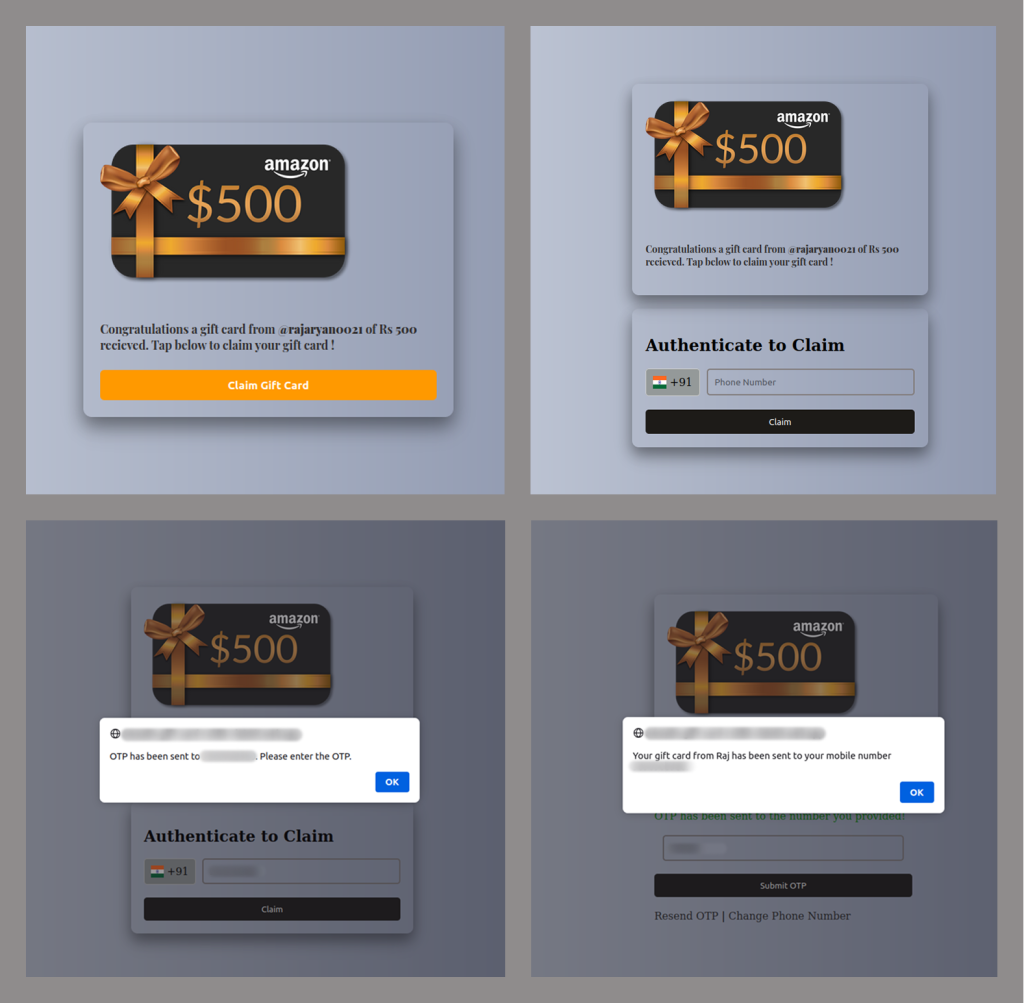
A phishing scheme aimed at getting OTP codes
Fraudsters often trick users into “verifying” their accounts by sending fake security alerts or urgent messages claiming suspicious activity. Victims are directed to a counterfeit page resembling platforms like eBay, where entering data (for example, credentials, payment data or documents) hands them over to scammers.
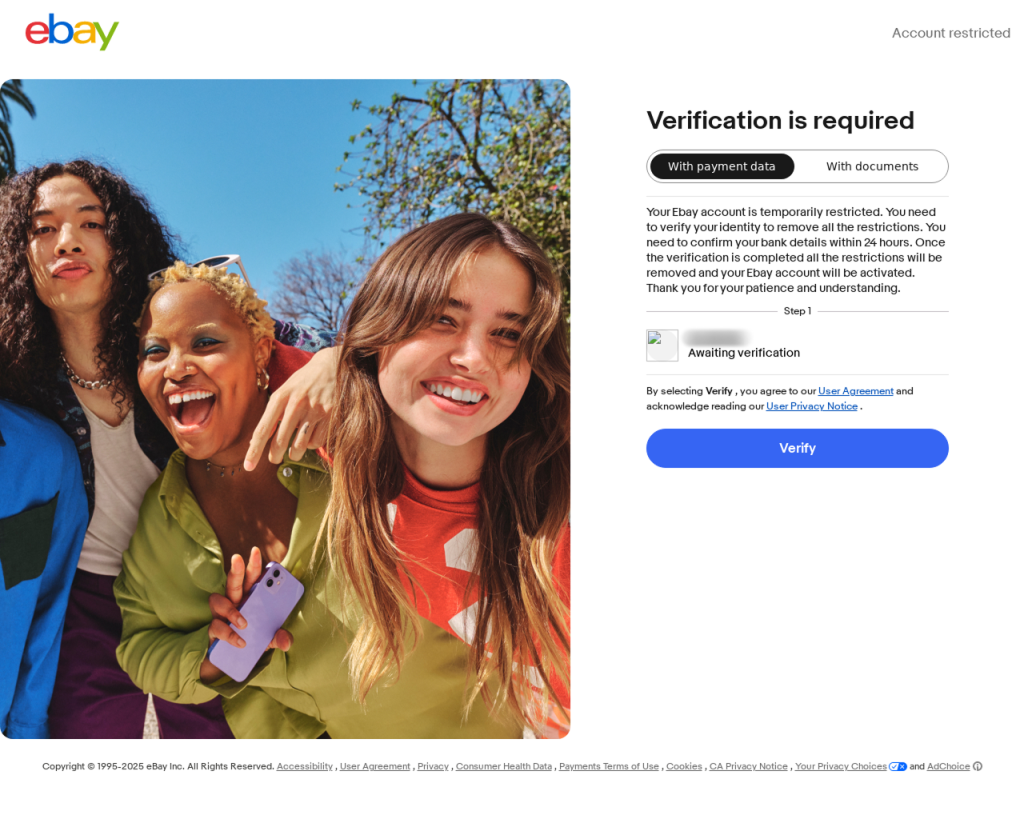
An example of a phishing site that mimics eBay
Another common tactic involves creating fake storefronts or seller profiles on marketplaces, listing numerous products at seemingly irresistible prices. Shoppers drawn in by the deals unknowingly provide payment details, only to receive nothing in return.
An example of a scam site that mimics an online marketplace
While many pages mimicking online stores target shoppers, there are others that are designed to collect business account credentials. For example, below you can see a phishing page targeting users registered on the Amazon Brand Registry platform, which provides businesses with a range of brand-building and intellectual property protection tools.
An example of a phishing page targeting Amazon brand accounts
Payment system phishing
Payment systems were mimicked in 19.27% of financial phishing attacks detected and blocked by Kaspersky products in 2024 – almost the same percentage as in 2023. Once again, PayPal was the most targeted, but its share of attacks fell from 54.73% to 37.53%. Attacks targeting Mastercard went in the opposite direction, nearly doubling from 16.58% in 2023 to 30.54%. American Express, Qiwi and Cielo are all new entrants into the top five, replacing Visa, Interac and PayPay.
TOP 5 payment systems mimicked by phishing and scam pages, 2024 (download)
Cryptocurrency scams
In 2024, the number of phishing and scam attacks relating to cryptocurrencies continued to grow. Kaspersky anti-phishing technologies prevented 10,706,340 attempts to follow a cryptocurrency-themed phishing link, which was approximately 83.37% higher than the 2023 figure of 5,838,499 (which itself was 16% bigger than the previous year’s). As cryptocurrencies continue to grow, this number is only ever going to get larger.
Financial PC malware
In 2024, the decline in users affected by financial PC malware continued. On the one hand, people continue to rely on mobile devices to manage their finances. On the other hand, some of the most prominent malware families that were initially designed as bankers had not used this functionality for years, so we excluded them from these statistics. As a result, the number of affected users dropped significantly from 312,453 in 2023 to 199,204 in 2024.
Changes in the number of unique users attacked by banking malware in 2024 (download)
Key financial malware actors
The notable strains of banking Trojans in 2024 included ClipBanker (62.9%), Grandoreiro (17.1%), CliptoShuffler (9.5%) and BitStealer (1.3%). Most of these Trojans specifically target crypto assets. However, Grandoreiro is a full-fledged banking Trojan that targeted 1700 banks and 276 crypto wallets in 45 countries and territories around the globe in 2024.
Name
%*
ClipBanker
62.9
Grandoreiro
17.1
CliptoShuffler
9.5
BitStealer
1.3
* Unique users who encountered this malware family as a percentage of all users attacked by financial malware
Geography of PC banking malware attacks
To highlight the countries where financial malware was most prevalent in 2024, we calculated the share of users who encountered banking Trojans in the total number attacked by any type of malware in the country. The following statistics indicate where users are most likely to encounter financial malware.
As in 2023, the highest share of banking Trojans was registered in Afghanistan, where it rose from 6% to 9% in 2024. Turkmenistan was next (as in 2023), where the figure rose from 5.2% to 8.8%, and Tajikistan was in third place (again), where the figure rose from 3.7% to 6.2%.
TOP 20 countries by share of attacked users
Country*
%**
Afghanistan
9.2
Turkmenistan
8.8
Tajikistan
6.2
Syria
2.9
Yemen
2.6
Kazakhstan
2.5
Switzerland
2.3
Kyrgyzstan
2.2
Uzbekistan
2.1
Mexico
1.6
Angola
1.5
Mauritania
1.5
Nicaragua
1.5
Guatemala
1.3
Argentina
1.1
Paraguay
1.1
Burundi
1.1
Bolivia
1
Uruguay
1
Belarus
0.9
* Excluded are countries and territories with relatively few (under 10,000) Kaspersky users.
** Unique users whose computers were targeted by financial malware as a percentage of all Kaspersky users who encountered malware in the country.
Types of attacked users
Attacks on consumers accounted for 73.69% of all financial malware attacks in 2024, up from 61.2% in 2023.
Financial malware attack distribution by type (corporate vs consumer), 2022–2023 (download)
Mobile banking malware
The statistics for 2023 provided in this section were retrospectively revised and may not coincide with the data from the previous year’s report.
In 2024, the number of users who encountered mobile banking Trojans grew 3.6 times compared to 2023: from 69,200 to 247,949. As can be seen in the graph below, the malicious activity increased dramatically in the second half of the year.
Number of Android users attacked by banking malware by month, 2022–2023 (download)
The most active Trojan-Banker family in 2024 was Mamont (36.70%). This malware first appeared at the end of 2023 and is distributed mostly in Russia and the CIS. Its distribution schemes are ranging from ages-old “Is that you in the picture?” scams to complex social engineering plots with fake stores and delivery tracking apps.
Verdict
%* 2023
%* 2024
Difference in p.p.
Change in ranking
Trojan-Banker.AndroidOS.Mamont.bc
0.00
36.70
+36.70
Trojan-Banker.AndroidOS.Agent.rj
0.00
11.14
+11.14
Trojan-Banker.AndroidOS.Mamont.da
0.00
4.36
+4.36
Trojan-Banker.AndroidOS.Coper.a
0.51
3.58
+3.07
+30
Trojan-Banker.AndroidOS.UdangaSteal.b
0.00
3.17
+3.17
Trojan-Banker.AndroidOS.Agent.eq
21.79
3.10
-18.69
-4
Trojan-Banker.AndroidOS.Mamont.cb
0.00
3.05
+3.05
Trojan-Banker.AndroidOS.Bian.h
23.13
3.02
-20.11
-7
Trojan-Banker.AndroidOS.Faketoken.z
0.68
2.96
+2.29
+18
Trojan-Banker.AndroidOS.Coper.c
0.00
2.84
+2.84
* Share of unique users who encountered this malware as a percentage of all users of Kaspersky mobile security solutions who encountered banking threats
The Bian.h variant (3.02%) that prevailed in 2023 dropped to eighth place, losing over 20 p.p., and several more new samples entered the ranking: Agent.rj (11.14%) at the second place, UdangaSteal.b (3.17%) and Coper.c (2.84%).
Geography of the attacked mobile users
Same as 2023, Turkey was the number one country targeted by mobile banking malware. The share of users encountering financial threats there grew by 2.7 p.p., reaching 5.68%. Malicious activity also increased in Indonesia (2.71%), India (2.42%), Azerbaijan (0.88%), Uzbekistan (0.63%) and Malaysia (0.29%). In Spain (0.73%), Saudi Arabia (0.63%), South Korea (0.30%) and Italy (0.24%), it decreased.
Country*
%**
Turkey
5.68
Indonesia
2.71
India
2.42
Azerbaijan
0.88
Spain
0.73
Saudi Arabia
0.63
Uzbekistan
0.63
South Korea
0.30
Malaysia
0.29
Italy
0.24
* Countries and territories with relatively few (under 25,000) Kaspersky mobile security users have been excluded from the rankings.
** Unique users attacked by mobile banking Trojans as a percentage of all Kaspersky mobile security users in the country.
Conclusion
In 2024, financial cyberthreats continued to evolve, with cybercriminals deploying phishing, malware and social engineering techniques to exploit individuals and businesses alike. The rise in cryptocurrency-related scams and mobile financial malware highlights the need for continuous vigilance and proactive cybersecurity measures, including multi-factor authentication, user awareness training and advanced threat detection solutions. As the digital finance landscape expands, staying ahead of emerging threats remains critical.
To protect your devices and finance-related accounts:
- Use multifactor authentication, strong unique passwords and other secure authentication tools.
- Do not follow links in suspicious messages, and double-check web pages before entering your secrets, be it credentials or banking card details.
- Download apps only form trusted sources, such as official app marketplaces.
- Use reliable security solutions capable of detecting and stopping both malware and phishing attacks.
To protect your business:
- Update your software in a timely manner. Pay particular attention to security patches.
- Improve your employees’ security awareness on a regular basis, and encourage safe practices, such as proper account protection.
- Implement robust monitoring and endpoint security.
- Implement strict security policies for users with access to financial assets, such as default deny policies and network segmentation.
- Use threat intelligence services from trusted sources to stay aware of the latest threats and cybercrime trends.
Source:: Securelist
