
You’ve probably never heard of “16Shop,” but there’s a good chance someone using it has tried to phish you.
A 16Shop phishing page spoofing Apple and targeting Japanese users. Image: Akamai.com.
The international police organization INTERPOL said last week it had shuttered the notorious 16Shop, a popular phishing-as-a-service platform launched in 2017 that made it simple for even complete novices to conduct complex and convincing phishing scams. INTERPOL said authorities in Indonesia arrested the 21-year-old proprietor and one of his alleged facilitators, and that a third suspect was apprehended in Japan.
The INTERPOL statement says the platform sold hacking tools to compromise more than 70,000 users in 43 countries. Given how long 16Shop has been around and how many paying customers it enjoyed over the years, that number is almost certainly highly conservative.
Also, the sale of “hacking tools” doesn’t quite capture what 16Shop was all about: It was a fully automated phishing platform that gave its thousands of customers a series of brand-specific phishing kits to use, and provided the domain names needed to host the phishing pages and receive any stolen credentials.
Security experts investigating 16Shop found the service used an application programming interface (API) to manage its users, an innovation that allowed its proprietors to shut off access to customers who failed to pay a monthly fee, or for those attempting to copy or pirate the phishing kit.
16Shop also localized phishing pages in multiple languages, and the service would display relevant phishing content depending on the victim’s geolocation.

Various 16Shop lures for Apple users in different languages. Image: Akamai.
For example, in 2019 McAfee found that for targets in Japan, the 16Shop kit would also collect Web ID and Card Password, while US victims will be asked for their Social Security Number.
“Depending on location, 16Shop will also collect ID numbers (including Civil ID, National ID, and Citizen ID), passport numbers, social insurance numbers, sort codes, and credit limits,” McAfee wrote.
In addition, 16Shop employed various tricks to help its users’ phishing pages stay off the radar of security firms, including a local “blacklist” of Internet addresses tied to security companies, and a feature that allowed users to block entire Internet address ranges from accessing phishing pages.
The INTERPOL announcement does not name any of the suspects arrested in connection with the 16Shop investigation. However, a number of security firms — including Akamai, McAfee and ZeroFox, previously connected the service to a young Indonesian man named Riswanda Noor Saputra, who sold 16Shop under the hacker handle “Devilscream.”
According to the Indonesian security blog Cyberthreat.id, Saputra admitted being the administrator of 16Shop, but told the publication he handed the project off to others by early 2020.
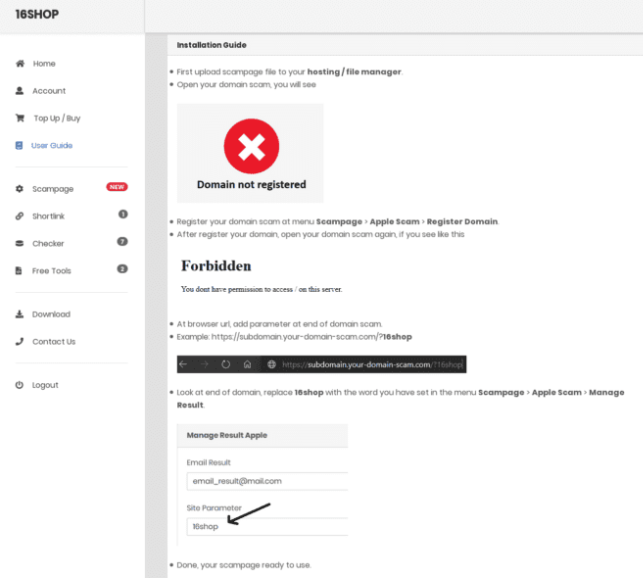
16Shop documentation instructing operators on how to deploy the kit. Image: ZeroFox.
Nevertheless, Cyberthreat reported that Devilscream was arrested by Indonesian police in late 2021 as part of a collaboration between INTERPOL and the U.S. Federal Bureau of Investigation (FBI). Still, researchers who tracked 16Shop since its inception say Devilscream was not the original proprietor of the phishing platform, and he may not be the last.
RIZKY BUSINESS
It is not uncommon for cybercriminals to accidentally infect their own machines with password-stealing malware, and that is exactly what seems to have happened with one of the more recent administrators of 16Shop.
Constella Intelligence, a data breach and threat actor research platform, now allows users to cross-reference popular cybercrime websites and denizens of these forums with inadvertent malware infections by information-stealing trojans. A search in Constella on 16Shop’s domain name shows that in mid-2022, a key administrator of the phishing service infected their Microsoft Windows desktop computer with the Redline information stealer trojan — apparently by downloading a cracked (and secretly backdoored) copy of Adobe Photoshop.
Redline infections steal gobs of data from the victim machine, including a list of recent downloads, stored passwords and authentication cookies, as well as browser bookmarks and auto-fill data. Those records indicate the 16Shop admin used the nicknames “Rudi” and “Rizki/Rizky,” and maintained several Facebook profiles under these monikers.
It appears this user’s full name (or at least part of it) is Rizky Mauluna Sidik, and they are from Bandung in West Java, Indonesia. One of this user’s Facebook pages says Rizky is the chief executive officer and founder of an entity called BandungXploiter, whose Facebook page indicates it is a group focused mainly on hacking and defacing websites.
A LinkedIn profile for Rizky says he is a backend Web developer in Bandung who earned a bachelor’s degree in information technology in 2020. Mr. Rizky did not respond to requests for comment.

Source:: KrebsOnSecurity
